A successful data breach can ruin a brand’s reputation in the competitive online world. Though some companies can salvage their reputation and remain relevant in their industry, many never recover from a data breach. You should never assume that your disaster recovery plan will be able to save your company if this type of disaster occurs.
In fact, you should be tightening your cybersecurity measures across all online touchpoints and invest in preventive measures. This blog explores the anatomy of a data breach, what it can look like, and what you can do to keep your brand and your customers safe.
Here’s what you need to know.
What does a data breach look like?
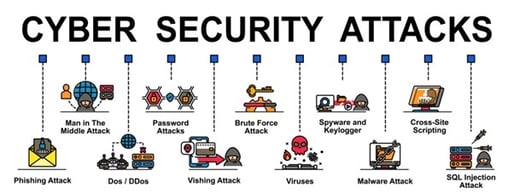
Before we get into the concrete cybersecurity measures you should implement in your organisation, let’s take a look at what a data breach could look like. Keep in mind that numerous types of cyber threats could lead to a data breach, including:
- Malware attacks
- Phishing scams
- DoS and DDoS attacks
- Password attacks
- Old account break-ins
- SQL injection attacks
- Internal security weaknesses
- Integration vulnerabilities
- Ransomware attacks
- And more
Prevention is always the best course of action, but if a data breach does occur, then the crucial next steps are to:
- Secure all user accounts, systems, and devices
- Localise the breach
- Notify all employees and customers
- Execute a disaster recovery plan
- Conduct PR damage control
- Strengthen your security measures and implement new ones
- Update your security protocols and policies
Now that you’re aware of the possible risks and the types of cyber-attacks that can occur, you’ll want to create a data breach disaster recovery plan. Below, we discuss some best practices to include in that plan, as well as strategies to put into effect before something happens to protect your small business from these threats.
1. Optimise your email security
Email security should be one of the top priorities for small businesses, as email communication can come with myriad cybersecurity risks - both for your employees and your customers. Keep in mind that email security threats come in many forms, ranging from phishing scams to malware content and executable files.
Both your employees and your customers are at risk from malicious emails. Big email clients like Outlook and Gmail have decent security measures, but you can help keep your employees safe by using alternative email apps that emphasise security and data protection. Combined with proper training, the right email app will help filter out suspicious emails and block malicious messages.

Remember that customer education is important as well. Be sure to educate your customers on phishing scams and what to look for in suspicious emails.
2. Secure your social media accounts
Corporate social media accounts can be subject to frequent online scams and cyber-attacks, and it's important to secure your social media channels to prevent data leaks and backdoor entry into your systems. For example, a backdoor to your social media accounts and tools could be an old user account left by one of your past employees.
You can eliminate this security risk by simply making sure to delete all user accounts or remote past employees from the accounts when new employees take their place. You should always keep all social media assets safe as well on a dedicated file uploading platform that scans files for malware and provides security for all assets.

Always use caution when clicking on suspicious links, and make sure to report any accounts that might be impersonating your brand. These accounts will reach out to your followers and try to scam them into giving away their sensitive data.
If left unchecked, these fake accounts can jeopardise your brand’s reputation.
3. Use strong passwords and two-factor verification
Unauthorised login attempts happen every day, as hackers and scammers are trying to work their way into your system, apps, and integrations through weak accounts and poor security measures. One of these poor security measures is a weak password, which you can strengthen simply by integrating a password manager into your processes.
Don’t trust your employees to come up with strong passwords or store them safely. Instead, use a trusted password tool.
Furthermore, it’s also important to enable two-factor verification for all your employees, their business accounts, and their devices. This will add a second security layer that'll prevent unauthorised logins, which, along with container monitoring and application management, is important for spotting suspicious activity that you can easily isolate and prevent from breaching your system.

4. Combine software and hardware firewalls
Businesses typically use software firewalls to protect individual devices in a network but combining these with a hardware firewall can help protect your network as a whole. A hardware firewall is a physical device that filters, monitors, and controls all the traffic in your network, acting as a gatekeeper between your devices and the outside world.
Modern hardware firewalls that have web gateway technology use early warning systems and can flag suspicious network activity, helping you to spot a potential cyber-attack early and prevent a data breach.
This can be especially useful when you’re conducting data migration, or when you're restructuring data flows and managing sensitive business and customer information. For growth-oriented businesses dealing with these processes and data types, a hardware firewall can be an indispensable security tool.

5. Regular security testing is a must
Penetration testing and regular dynamic application security testing should be essential processes in your overarching cybersecurity strategy. Only by regularly testing the security measures and policies you have in place will you be able to keep up with new industry trends and spot potential vulnerabilities.
Security testing is one of the best ways to prevent cyber-attacks and avoid having to execute a costly disaster recovery plan. You can conduct security testing in-house or you can hire external cybersecurity consultants and IT experts.
These are the types of cybersecurity testing you can conduct in your organisation:
- Vulnerability monitoring and testing
- Penetration testing
- General security scanning
- Dynamic application security testing
- Security risk assessment
- Ethical hacking
- Posture assessment
- Cybersecurity policy assessment
Over to you
It only takes one successful data breach to jeopardise your brand’s reputation and drive customers away for good. While you should have a comprehensive disaster recovery plan, you should focus primarily on preventing data breaches and minimising cybersecurity risks in your organisation.
Use these tips to plug any security holes and keep your brand, your employees, and your customers safe.
Author’s Bio:
Nikola is a seasoned brand developer, a writer, and a storyteller. He loves exploring new topics to turn into engaging stories for the online community.

